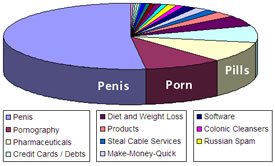
Among the most ominous threats facing online users today are fraudulent sites designed to appear as real e-commerce web sites and fool un savvy internet surfers into divulging personal information. These copycat sites, which are often perfect imitations of the legitimate site, are home base for phishers– the word used to describe hackers who build these “phishing” sites to fool users into divulging personal information such as user name, social security number, password or credit card numbers. This information is then either sold or used by the hackers themselves to exploit unwary consumers. According to the Anti-Phishing Working Group (APWG), an organization devoted to reporting on and ultimately thwarting this illegal activity, at least 5% of users are fooled by the spoofed sites and suffer the consequences of credit card fraud, identity theft and financial loss. In their year-end report, APWG reported a steady increase in spoofed sites, which grew at a rate of an astonishing 24% per month throughout 2004. Growth in this area is expected to continue in 2005.
 |
They also report that financial institutions are by far the most frequently targeted enterprises, accounting for nearly 75% of counterfeit Web sites. Another industry targeted by phishers are ISP's, which made up 16% of the phishing sites uncovered by APWG’s research. More Sophisticated Phishing In a related CNN story published in January 2005, reported that phishing attacks are also getting more sophisticated as they proliferate. Although the image of the lone hacker working his mischief in solitude may be the current stereotype, the CNN story characterized the new wave of phishers as more akin to organized crime than petty criminals devising isolated attacks. This more sinister threat comes in the form of highly coordinated offensives from sources in the U.S., Russia and other countries. Their increasingly complex methods have elevated the stakes as e-commerce enterprises rush to try and secure their network assets and keep their customers protected.
Different than a typical phishing attack, where fraudsters send out hundreds of thousands of e-mails (SPAM) and hope for the best results possible, personalized phishing attacks target individual named account holders at specific banks. The more organized attacks appear on the surface to be common phishing events where users are directed to a spoofed site that looks legitimate. Unlike regular phishing sites however, these URL's are hosts to malicious applications that plant code in the visitor’s computer. Once infected with mal-ware (malicious applications), even if users leave the phishing site without giving any information, they won’t be safe.
 |
The next time they try to access the legitimate site by typing the Web address into a browser, the malware automatically redirects them to the fraudulent site. Since an accurate URL was entered, users have no idea they are at a phishing site. The CNN article states that this method was used successfully in attacks spoofing several South American banks. In those attacks, phishers took advantage of a Microsoft vulnerability on machines that had not been re mediated by patching. The implications are sobering for everyone. Imagine typing your bank’s URL into your browser and not knowing if you are at the legitimate site or not!
By now, most of us are familiar with phishing attacks and likely have seen one or two of these fraudulent communications. They might be emails that tell us our bank, ebay or Paypal account needs updating. Inside a typical message, there is a link to what looks like an official Web site but is actually a scam, some of them authentic-looking, than others. The phony web site is designed to gather your personal account information, passwords, Social Security number and other information useful to thieves. Fortunately, most of us notice the bogus URL or the awkwardness of the content before any real damage can be done. Some of these emails even imply that you actually have an account at the listed internet site in an effort to gain that same information.
Domain hijacking is the practice of stealing an organization or individual web site name. This method typically relies on the victim’s lack of vigilance. In a common scenario, perpetrators send a phony or misleading registration transfer approval form, or a fraudulent transfer authorization to a web site owner.
These are usually timed to coincide with domain name renewals. Unwitting victims automatically ok the transfer or authorization, thinking it’s a legitimate renewal notice. In a related scam, cyber squatters purchase domain names that are identical to existing web site addresses except for one or two letters and wait for visitors to misspell addresses. And it’s hard to tell when you’ve been spoofed. Cyber criminals build web sites that are usually remarkably identical to the real ones. Visitors enter their personal data, thinking nothing is awry and the crime ensues.
Related:
Phishing Hole Discovered in Internet Explorer
Avoiding a Phishing Attack
Internet Cookies
Pharming for Your Identity
Hackers, Beyond the Browser
|